Bio-Security
We are passionate about what we do
Talk to us. We'd like to work with you.
Types of Bio-Security
Bio-Security
We offer professional bio-security installation and maintenance services across Manhattan, Brooklyn, Queens, Bronx, Staten Island, and surrounding areas.
Each bio-security solution offers distinct advantages and limitations, depending on its intended purpose and the environment in which it is deployed. At Safeco, we provide expert consultation to help you select the most effective placement options, ensuring the establishment of a secure perimeter. Strategic placement is essential to achieving optimal security outcomes.
Our company specializes in providing advanced biometric security systems for residential, commercial, industrial, corporate, and business clients. Biometric security solutions offer a wide range of applications, including biometric safes, access control systems, fingerprint scanners, biometric USB devices, attendance and authentication systems, and biometric entry solutions. We partner with leading brands in the industry and are proud to be one of the few professional integrators in your area.

Fingerprint Recognition

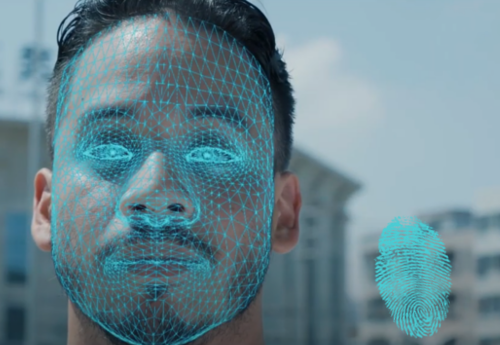
Facial Recognition

Temperature Detection
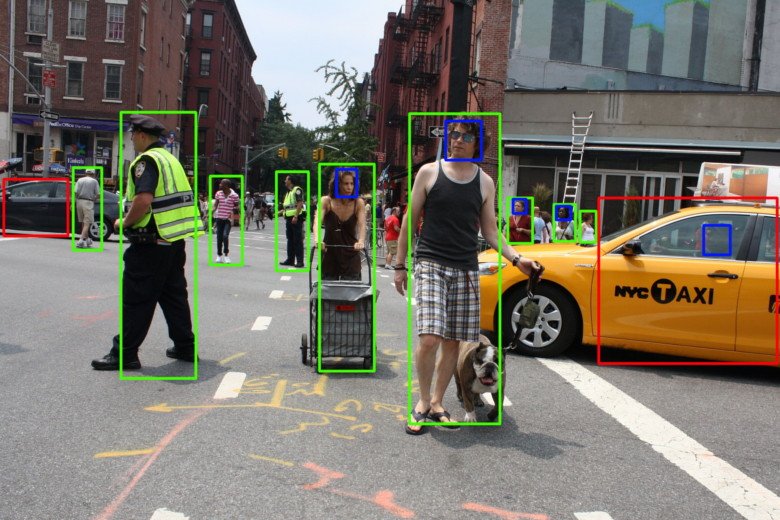
Behavior Analysis System
Additional Information:
What is Bio-Security?
Bio-security refers to biometric security solutions that control access based on unique biological traits. Once costly, biometric technology is now more affordable and widely accessible. Common examples include fingerprint, palm vein, facial recognition, iris scanning, voice recognition, and more.
How is Bio-Security used?
Biometric security provides significant advantages over traditional methods by using unique biological traits, like fingerprints or facial recognition, to authenticate individuals. This makes it nearly impossible to fake. For example, in time and attendance systems, it eliminates clock-in fraud because employees must be physically present to log in. The same applies to restricted access areas—only authorized individuals can enter, as their biological traits act as their "key." Biometric systems can work alone or with other security devices. One of the latest uses is temperature detection, where users with high temperatures are denied access, and monitoring staff is alerted.
Our Industry Partners






